| Section |
|---|
| Column |
|---|
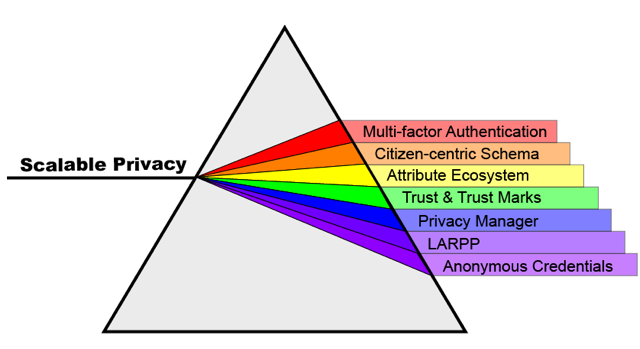
Scalable Privacy: An NSTIC Pilot for the Identity Ecosystem |
|
...
...
Attribute Registries, Bundles and Application Categories
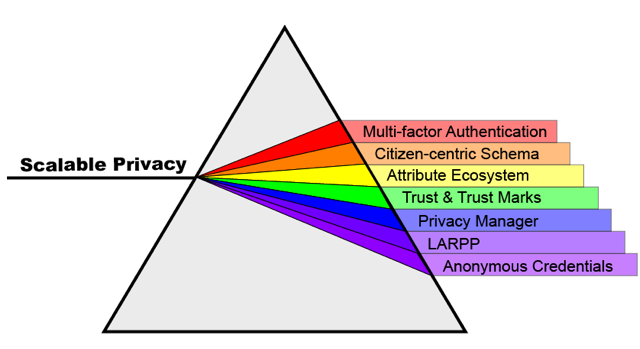 Image Added Image Added
|
|
| Info |
|---|
| title | A Note on Terminology |
|---|
|
On these pages we will often group applications into application categories. It will sometimes be useful to group attributes into various attribute bundles based on their common applicability to a set of use cases. A given attribute bundle may be associated with a particular application category when the attributes in that bundle are generally required or useful for the operation of applications in that category. |
The National Strategy for Trusted Identities in Cyberspace (NSTIC) initiative is a "White House initiative to work collaboratively with the private sector, advocacy groups and public-sector agencies" with the goal of advancing the "NSTIC vision that individuals and organizations adopt secure, efficient, easy-to-use, and interoperable identity credentials to access online services in a way that promotes confidence, privacy, choice and innovation." The Internet2 Scalable Privacy Project (ScalePriv) is one of five pilot projects to receive funding from the first round of pilot funding in September 2012. The ScalePriv Project contains several major thrusts around identity and privacy, including a focus on: - Promoting the adoption of Multi-factor Authentication (MFA) across Higher Education institutions.
- Attribute ecosystem development: Attribute registries, bundles and entity categories.
- Citizen-Centric Schema.
- Privacy Manager.
- Anonymous Credentials.
- Lifestyles of the Attribute Rich and Privacy Preserved
|
Key focus areas of the ScalePriv Project
- Multi-Factor Authentication (MFA) in Higher Education – MFA Cohortium and Pilots. This is the original starting page for the two key thrusts within the MFA project focus area.
- MFA Cohortium - Current primary website for the MFA Cohortium effort
2. Trust and the Attribute Ecosystem
Periodic Table of Trust Elements
- Read Me (pdf)
- Periodic Table (pdf, draft 8-Nov-2013)
- NSTIC Principles and the Trust Elements they invoke - overview (pdf)
See GPII (see ISO/IEC 24751 parts 1-3, at http://standardswww.isoidecosystem.org/ittf/PubliclyAvailableStandards/index.html for their unbundled list)
The organizing concept of context in assessing privacy dimensions of online scenarios
- Reading Notes on Helen Nissenbaum's Privacy in Context: Technology, Policy, and the Integrity of Social Life
Class diagram for attributes, subject, relying party
Showing multiple types of attributes including those related to accessibility preferences of the subject
 Image Removed
Image Removed
"An example of how a variety of attributes can be provided to a replying party for proper presentation of a web site to an identity having specialized access needs."
credits: Access for all abstract model from ISO/IEC 24751-1
Use Case Library
Meetings, Workshops, and Conferences of Interest
- Internet Identity Workshop (IIW) - 23-25 October 2012, Mountan View CA
- IDESG Plenary Meeting - 29-30 October 2012, Washington D.C.
Reference docs
3. Citizen-Centric Schema
4. Privacy Manager
5. Lifestyles of the Attribute Rich and Privacy Preserved
6. Anonymous Credentials
Supporting and Reference materials
...