Versions Compared
Key
- This line was added.
- This line was removed.
- Formatting was changed.
Jump to:
| Table of Contents | ||||||||
|---|---|---|---|---|---|---|---|---|
|
The SP SSO Settings section in Federation Manager is where a Site Administrator configures the key Service Provider (SP) service endpoints found in the SAML metadata's SPSSODescriptor element. These include:
- Assertion Consumer Service endpoints (
<AssertionConsumerService>),also known as ACS URLs - Discovery Response locations (
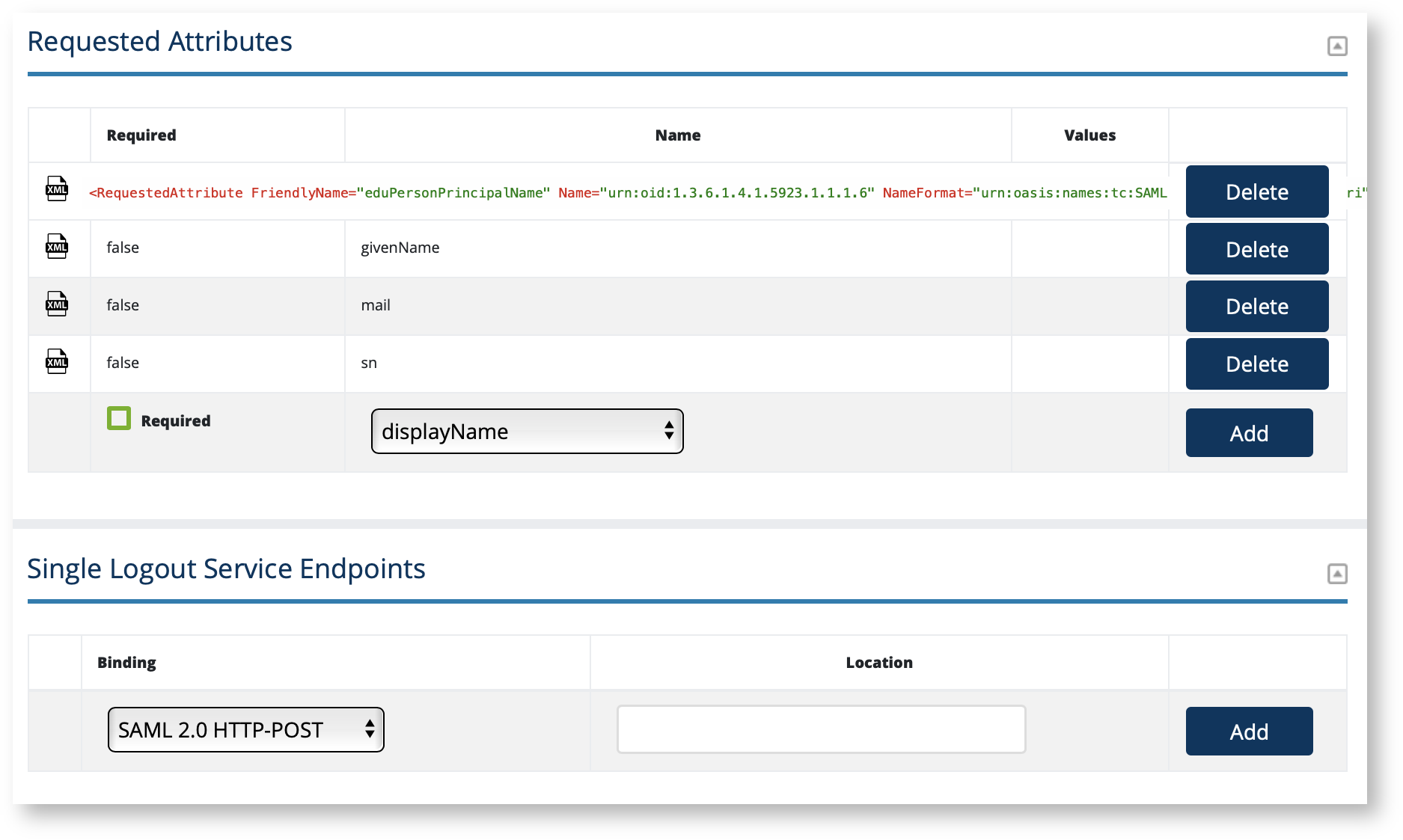
<SingleSignOnService>) - Requested Attributes (
<RequestedAttribute>elements within<AttributeConsumingService>) - Single Logout Service endpoints(
<SingleLogoutService>).
To configure:
Login to Federation as a Site Administrator
Click on the entity you wish to update to bring up the View/Edit page.
On the left navigation, click "SP SSO Settings".
Enter information as directed as shown in the "SP SSO Settings" section.
Click the XML toggle icon to preview the data you've entered as shown in SAML.
Use the toggle in the Index column to manually order your ACS URLs and Discovery Response endpoints.
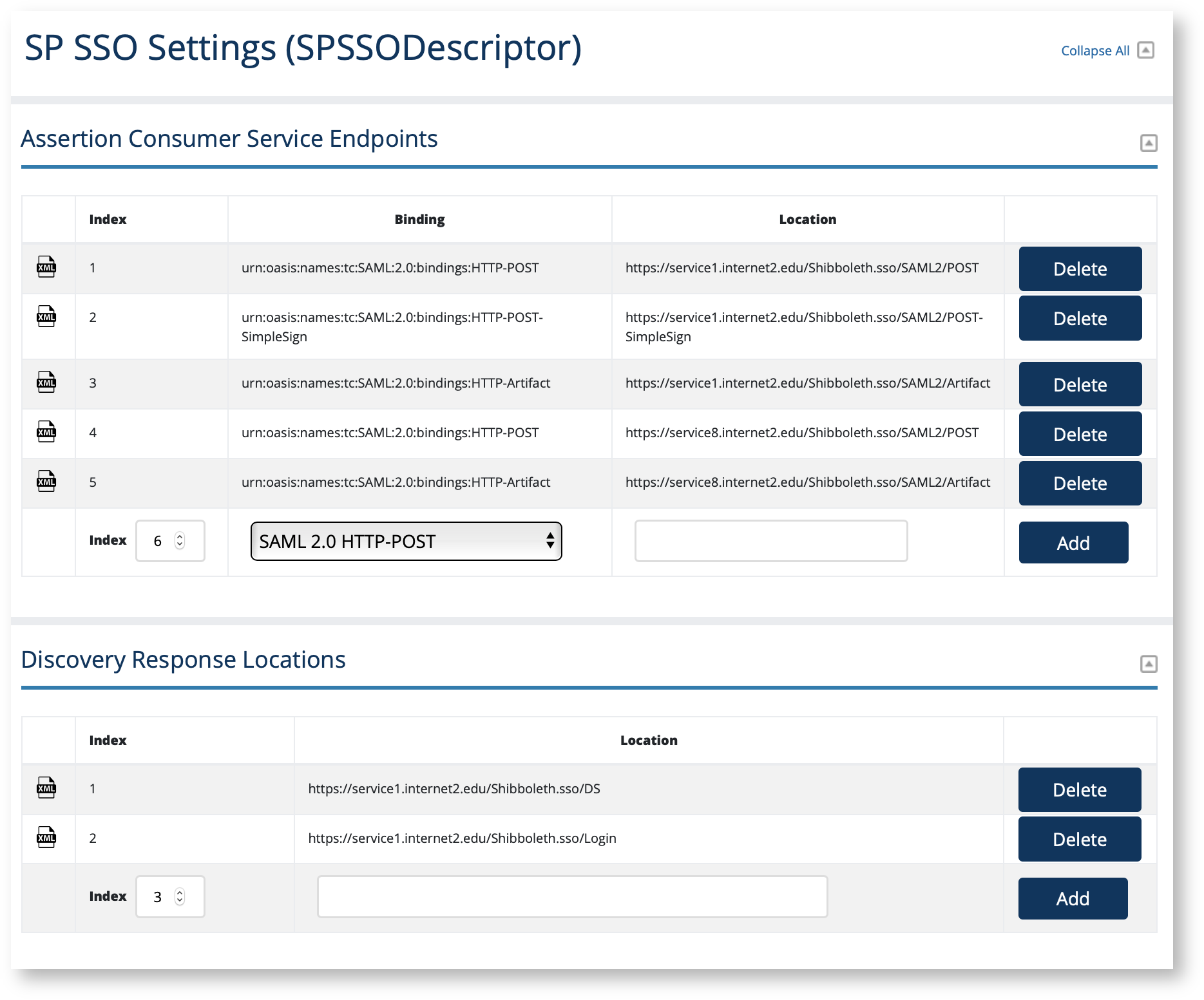
AssertionConsumerService endpoint (ACS URL) requirements
All <AssertionConsumerService> endpoints MUST begin with https://, that is, an Assertion Consumer Service endpoint, or ACS URL, must be encrypted with modern, supported TLS encryption.
A SP in the Incommon Federation MUST include at least one <AssertionConsumerService> endpoint with a SAML2 HTTP-POST binding.
DO NOT register any SAML1 endpoints. SAML1 is deprecated. The option is available for legacy support only.
See Section 5.1: Web Browser SSO Profile in the Security Assertion Markup Language (SAML) V2.0 Technical Overview.
Should I configure a DiscoveryResponse location?
If you have configured your SP to use a Discovery Service via the SAML V2.0 Identity Provider Discovery Protocol, you MUST include at least one <DiscoveryResponse> endpoint in your SP metadata. A Discovery Service will redirect the user back to you at the designated endpoint once they have selected their preferred identity provider.
Configuring Requested Attributes
Configuring Requested Attributes is optional.
Federation Manager lets you select from a list of commonly supported attributes in the Incommon Federation when configuring Requested Attributes.
To learn more, see saml-metadata-requested-attributes.
Should I configure a SingleLogout endpoint?
If you have configured your SP to send single logout (SLO) requests to an IdP advertising a SingleLogoutService endpoint, you must publish your SP's SingleLogoutService endpoint in your published metadata. Failing to do so will cause an error when the IdP attempts to respond to your SP's SLO request.
Shibboleth SP software is by default configured to send SLO requests.
Working with SAML metadata
| Content by Label | ||||||||
|---|---|---|---|---|---|---|---|---|
|
Related content
| Content by Label | ||||||||
|---|---|---|---|---|---|---|---|---|
|
Get help
Can't find what you are looking for?
| Button Hyperlink | ||||||||
|---|---|---|---|---|---|---|---|---|
|