| Section | ||||
|---|---|---|---|---|
|
| Info | ||
|---|---|---|
| ||
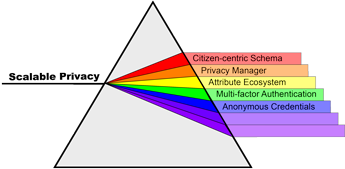
The National Strategy for Trusted Identities in Cyberspace (NSTIC) initiative is a "White House initiative to work collaboratively with the private sector, advocacy groups and public-sector agencies" with the goal of advancing the "NSTIC vision that individuals and organizations adopt secure, efficient, easy-to-use, and interoperable identity credentials to access online services in a way that promotes confidence, privacy, choice and innovation." The Internet2 Scalable Privacy Project (ScalePriv) is one of five pilot projects to receive funding from the first round of pilot funding in September 2012. The ScalePriv Project contains several major thrusts around identity and privacy, including a focus on:
Scalable Privacy Project Overview (PDF)Scalable Privacy Website |
Key focus areas of the ScalePriv Project
1. Multi-Factor Authentication
- Multi-Factor Authentication (MFA) in Higher Education – MFA Cohortium and Pilots. This is the starting page for the two key thrusts within the MFA project focus area.
2. Attribute ecosystem development
- Attribute Ecosystem slides (working draft)
- Working flows redux
- Ways of Looking at the Attribute Ecosystem (working hyper-poem)
- Version 1.0 of a browsable Multi-Schema Attribute Registry has been developed as part of this project.
- The information is also available in the form of a spreadsheet and a Protégé ontology project.
- An overview of the Attribute Registry is also available.
- Rutgers Identity Attribute Registry (PDF)
- LoA Profile Registry
Entity Categories
- R&S Category Bundle from InCommon
- SWAMID Entity Categories
- The Entity Category Attribute Specification (draft-macedir-entity-attribute)
3. Citizen-Centric Schema
- Citizen-centric Overview/Status slides (working draft)
- Attribute-Ecosystem-Annotated Use Cases
- Accessibility Support
4. Privacy Manager
- Privacy Manager Overview/Status slides (working draft)
- CMU Tech Report, Warning Design Guidelines, Bauer et al
- Informed Consent and Privacy Management
5. Anonymous credentials
Supporting and Reference materials
Use Case Library
Useful reference documents