| Include Page | ||||
|---|---|---|---|---|
|
In Grouper 2.6.6 there is a first pass at JEXL loaded groups. It is basic and can be built on.
We want to be able to craft policies by an expression instead of creating loaders or tons of reference groups based on cartesian products of basis/ref groups.
Individual groups can be configured to automatically have their membership managed with individual subject or other basis groups.subjects (or in future groups as members)
Why do we need this feature?
- Reduces pre-loaded rollups that might not be used
- You don't need a loader job for each one of these groups
- Any Grouper user could edit the policies if they can READ underlying groups. The expressions are secure (future state)
- The memberships of the ABAC groups are real time based on an intelligent change log consumer (future state)
- You can have a UI to help build it and give good error messages
- Could visualize the policies. Perhaps could be integrated into existing visualization (future state)
- This solved
- solves the issue of composites with any number of factors
Expressions
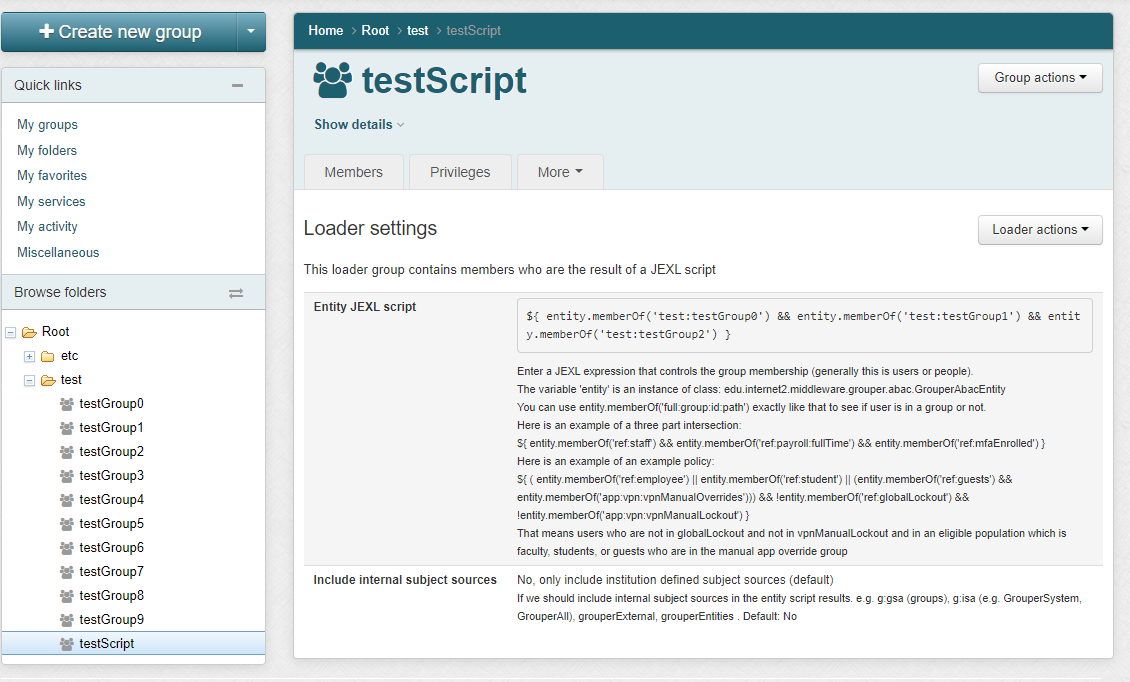
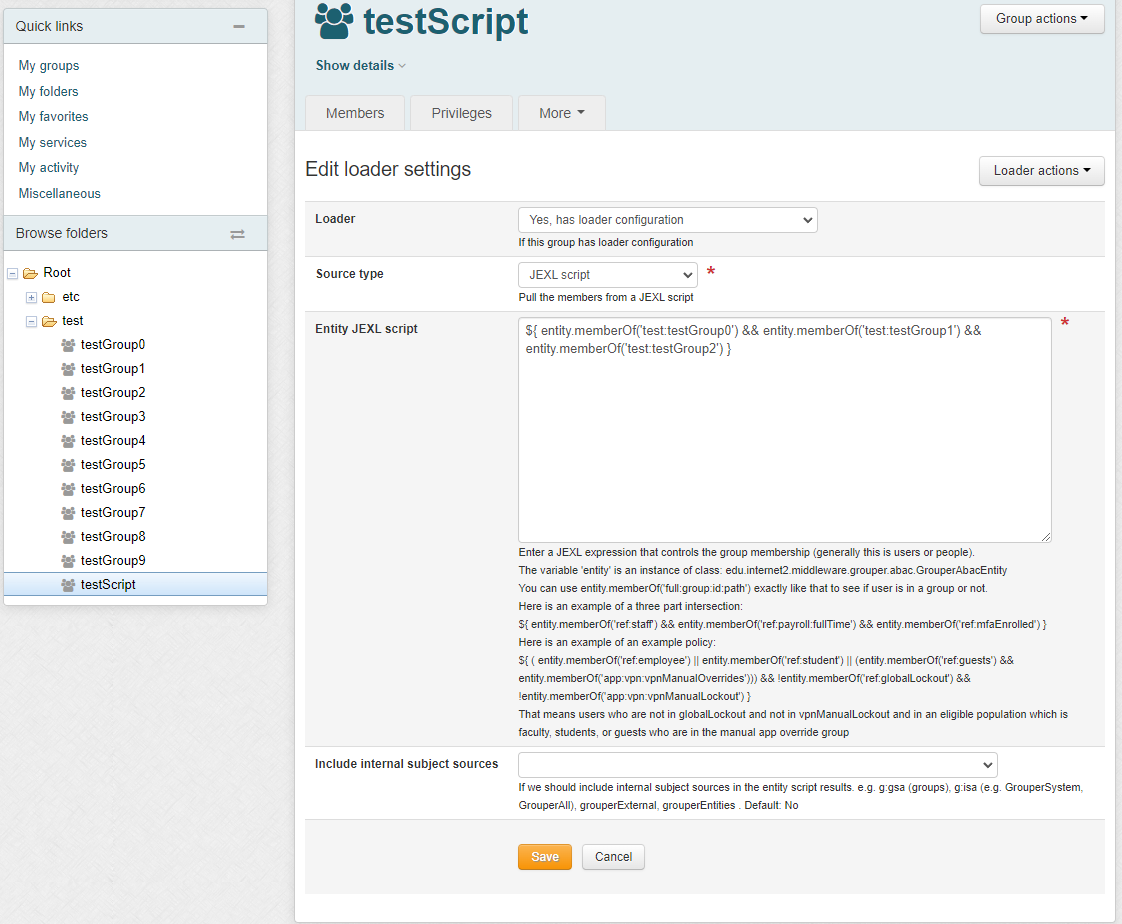
UI to configure
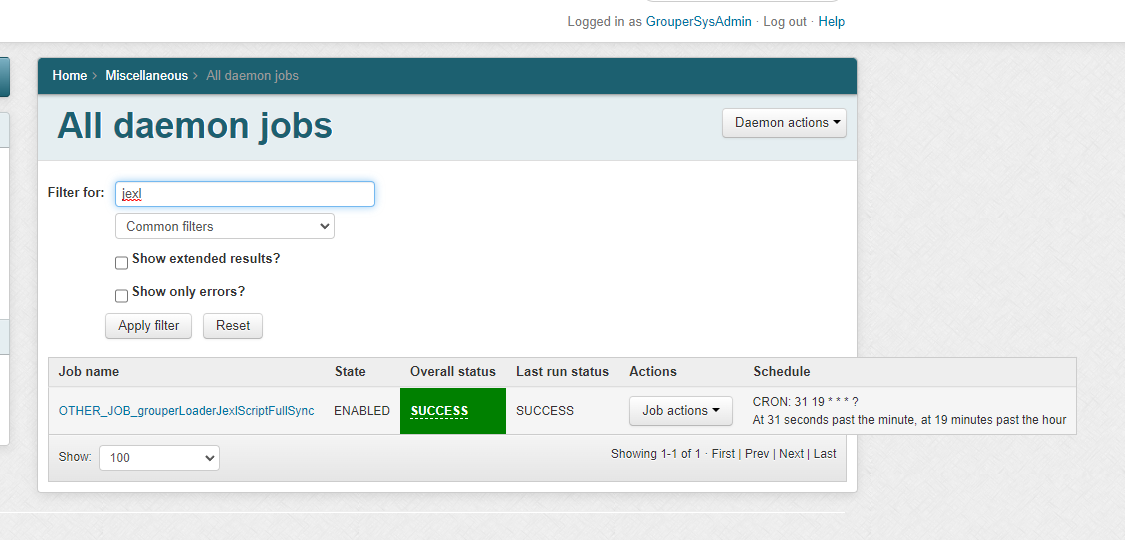
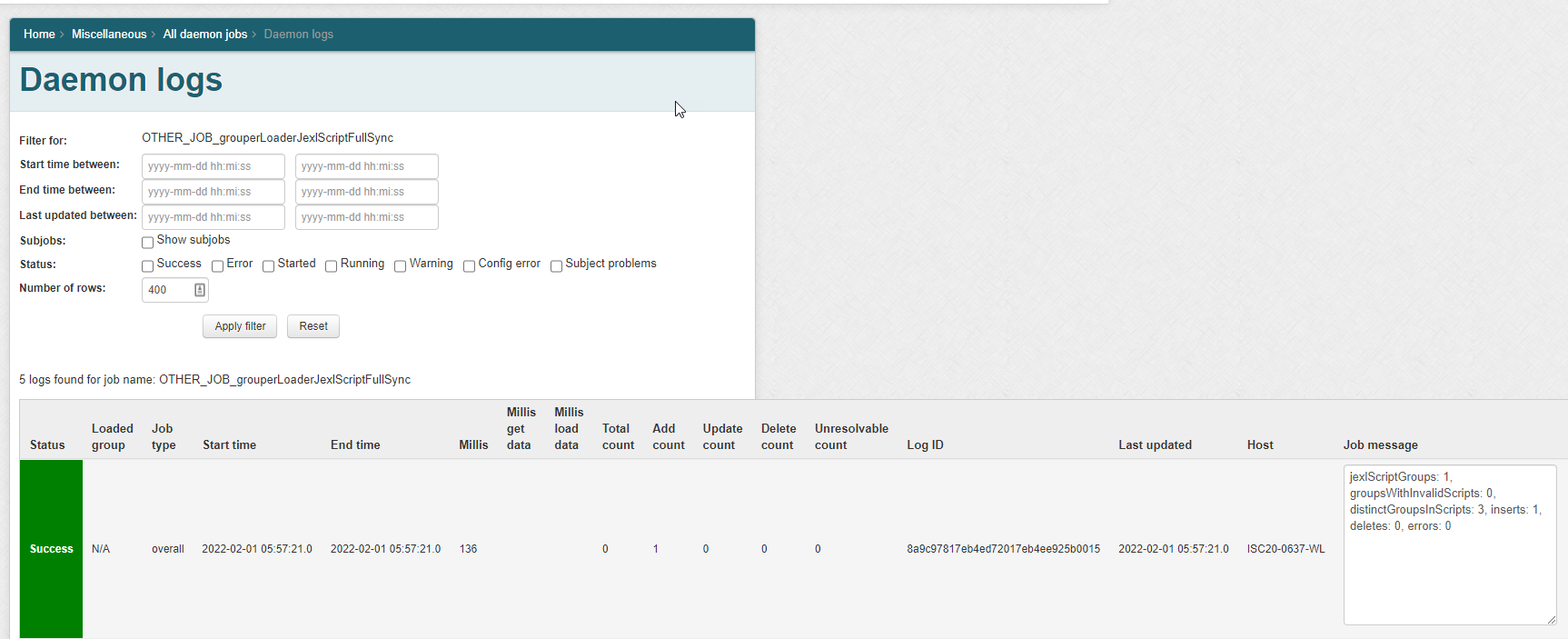
Daemon screen
Note in Grouper v2.6.6 you need to wait an hour after changing a script, or run the JEXL script loader full job. In the future we will have an incremental and run the full nightly
Scripts
The script The expression can only be written by people who can READ groups in the script and UPDATE the abac owner group/subject tables.
Boolean logic and wildcards are required
...
(group.campus =~ ['palmer', southern'] and group.termStart - 7 > sysdate and group.termEnd + 7 < sysdate)
or (person.primaryAffiliation =~ ['faculty', 'staff'] and person.dept =~ ['physics', 'math'])
...
Requirements for expressions
...
Needs to be parsed so we can
check security, do real-time
updates, and analyze policies
...
Seems like JEXL is a good place to start
Expression 1: Campus not in palmer or southern, and term start more than 7 days ago
| Code Block |
|---|
group.campus !~ ['palmer', 'southern'] and group.termStart - 7 > sysdate |
Tables
Two Grouper tables will be constructed for performance reasons (getting relationships and point-in-time)
...
These tables are managed by grouper based on configuration.
Group attribute table
The group attribute values come from the attribute framework which could be automatically fed from external systems of record. For now, an OtherJob could do this on a schedule.
...
Loading attributes to groups
This can use a similar format to the marker / name-value pair convention for attributes, or can just be attributes on groups. i.e. the marker attribute column is optional. Types will be converted (e.g. the varchar "24" will be converted to 24 if the attribute is integer based). Note: dates can be converted to the appropriate type (e.g. from date column to integer seconds from 1970)
...
. Since this is actually a JEXL script (not a JEXL expression), so you could have multiple lines, variables, conditionals, etc
In an entity script, the variable 'entity' is an instance of class: edu.internet2.middleware.grouper.abac.GrouperAbacEntity
You can use entity.memberOf('full:group:id:path') exactly like that to see if user is in a group or not.
Here is an example of a :<br /><br />Here is an example of am :<br /><br />
| Expression | Description |
|---|---|
| ${ entity.memberOf('ref:staff') && entity.memberOf('ref:payroll:fullTime') && entity.memberOf('ref:mfaEnrolled') } | Three part intersection |
${ ( entity.memberOf('ref:employee') || entity.memberOf('ref:student') || (entity.memberOf('ref:guests') && entity.memberOf('app:vpn:vpnManualOverrides'))) && !entity.memberOf('ref:globalLockout') && !entity.memberOf('app:vpn:vpnManualLockout') } | Example policy That means users who are not in globalLockout and not in vpnManualLockout |
TO DO
- Load groups as members
- Add incremental job
- Unit tests
- Better validation
- More methods to call (other than hasMember)
- Add subject attributes e.g. from global attribute resolver
- Failsafes
- Add delegated admin based on READ of groups
- Visualization
Parse expression with JEXL (for Grouper developers)
...
Subject attribute table
The individual attribute values are fed from basis/ref groups and the values can be transformed from the group name to something that has institutional meaning. This can happen from attribute or from text manipulation
...
Feed the expression through this simple program
...
| Expand | ||
|---|---|---|
|
Analyze policy
To confirm a policy is correct, a long form translation of the policy can be displayed along with group names and group counts
Full sync
A nightly full sync will occur. The incremental sync should stop. Make sure everything in the attribute tables is up to date. Make sure all the policy loaded groups are up to date.
Incremental sync
An incremental change log consumer can
- If group attributes change, see if it affects group attributes
- See which memberships change, if these are related to subject attributes, then update the attribute tables
- (future state)
- If attributes change, see which policies those refer to, and incrementally adjust the membership of those groups
- Policy changes should change the population
Loading groups that are used
...