UMD is running Grouper in production as of October 2016.
Timeline
- October 2016 - Deployed version 2.2.2 to production
- July 2017 - Upgraded to 2.3.0
- December 2019 - Upgraded to 2.4.0 with TIER docker containers, complete migration to AWS (ECS - Elastic Container Service)
Presentations
- Overview of UMD's Grouper implementation as of October 2018: UMD CCTG Grouper Fall 2018.pdf
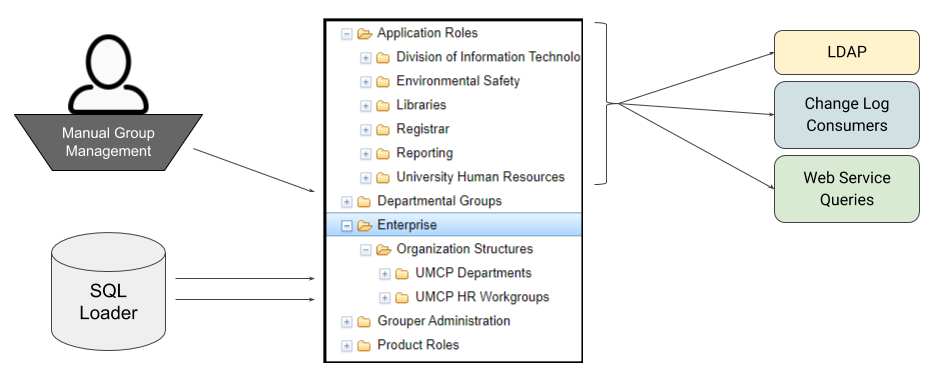
Organization
Structure of UMD folders at a high level.
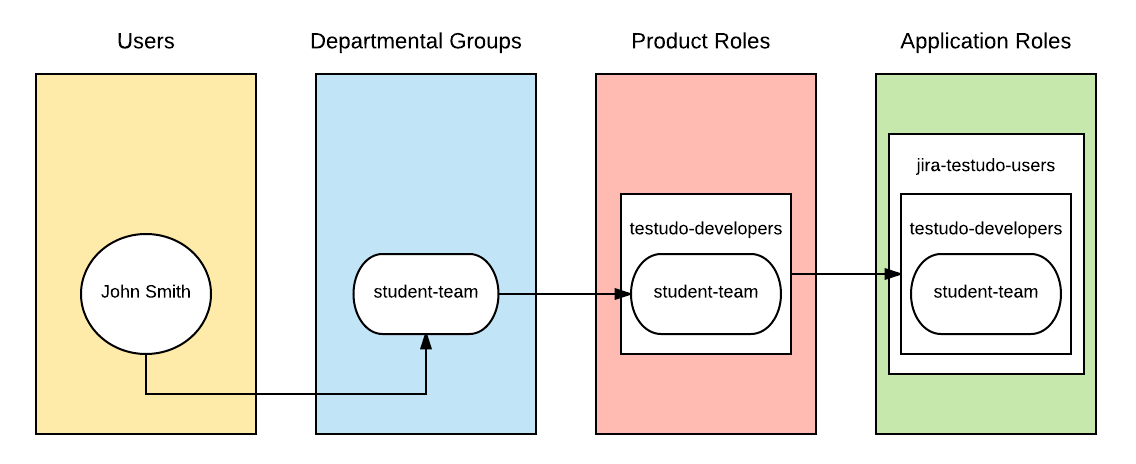
- Application Roles - groups which are provisioned or consumed by external applications to determine access
- Departmental Groups - groups which are created as-needed by users to link other groups together
- Enterprise - org structures generated by daily SQL loaders
- UMCP Departments
- UMCP HR Workgroups
- Product Roles - groups which are shared by application roles in a standard pattern
Integrations
- CAS authentication (Grouper UI)
- LDAP authentication (Grouper WS) (for Grouper WS principals)
- Custom Change Log Consumers
Atlassian JIRA
Atlassian Fisheye/Crucible
- SNS (Publish to AWS SNS topic for consumption by AWS Lambda functions)
- Consumers (mainly written in Node.js):
- LDAP Attributes (for writing ldap attributes in forms not yet supported by PSPNG as of March, 2020)
- Google Group Sync
- Consumers (mainly written in Node.js):
- Oracle Roles (Syncing Grouper developer groups into Oracle)
Database Updater for Tableau (decommissioned)
- Web Services
Tuition Remission
Environmental Safety
Other internal DIT Web Applications (like IDM Registry, an internal IAM webservice for person data)
- LDAP Provisioning (PSPNG)
- OpenLDAP
Atlassian Confluence
Atlassian Bamboo
Splunk
Business Office Ticketing System
Informatica Cloud
- Active Directory
- Secret Server
- Tableau
Build and Deployment
UMD has customized the standard 2.4 TIER docker container. We create our own base image on top of the TIER image with our custom Java code for things like health checks and other connectors.
We then overlay our grouper and container configuration from a another configuration repo to create the final image. In the configuration repo we do things like install mod_auth_cas for apache to handle CAS login. This image built with bamboo and deployed to AWS on ECS through Cloudformation.